Introduction
![[CM] [SIT] [E3] [RAR] [T2] Treatment and Control](https://no-cache.hubspot.com/cta/default/3893111/0d301475-ef94-4bba-bff2-c9a59521cd91.png) For the Singapore Institute of Technology (SIT), effective crisis readiness requires not only identifying threats but also implementing structured risk treatment and control measures.
For the Singapore Institute of Technology (SIT), effective crisis readiness requires not only identifying threats but also implementing structured risk treatment and control measures.
In alignment with the BCM methodology referenced in BCMpedia, risk treatment strategies are categorised as Risk Avoidance, Risk Reduction, Risk Transference, and Risk Acceptance, and are supported by existing and planned controls.
As a higher learning institution with distributed campuses, digital learning platforms, industry partnerships, and critical IT infrastructure, SIT must adopt a multi-layered control framework to manage operational disruptions.
Table Below: Notes for BCM Institute's Course Participants: This is the template for completing the "[CRA] Part 2: Treatment and Control."
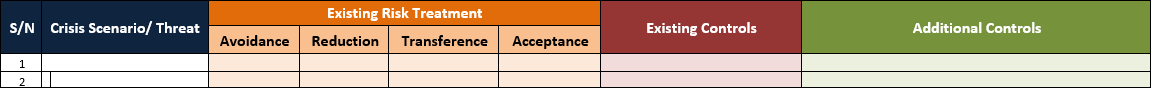
Part 2: CRA – Treatment and Control for SIT
The table below translates identified threats into actionable treatments and controls tailored to SIT’s academic, administrative, and digital ecosystem.
Table: Risk Treatment and Control
|
Type of Threats / Crisis Scenarios |
Existing Risk Treatment - Risk Avoidance |
Existing Risk Treatment - Risk Reduction |
Existing Risk Treatment - Risk Transference |
Existing Risk Treatment - Risk Acceptance |
Existing Controls |
Additional (Planned) Controls |
|
Flood (Campus / Facility) |
Avoid building critical facilities in flood-prone zones |
Installation of drainage systems, flood barriers |
Insurance coverage for property damage |
Accept minor localised flooding risks |
Campus drainage, facility monitoring systems |
Smart flood detection sensors, climate risk modelling |
|
Pandemic / Infectious Disease Outbreak |
Avoid high-density physical events during outbreaks |
Hybrid learning, safe distancing, health protocols |
Health insurance, outsourced medical services |
Accept manageable absenteeism |
Remote learning platforms, health advisories |
AI-driven health monitoring, pandemic playbooks |
|
Fire (Campus Buildings / Labs) |
Avoid hazardous material mismanagement |
Fire suppression systems, drills |
Property and liability insurance |
Accept residual fire risk |
Fire alarms, extinguishers, and evacuation plans |
Smart fire detection (IoT), enhanced lab safety controls |
|
Cyberattack (Ransomware / Data Breach) |
Avoid the use of insecure systems |
Network security, MFA, endpoint protection |
Cyber insurance, managed security services |
Accept low-level phishing attempts |
SOC monitoring, firewalls, and user awareness training |
Zero-trust architecture, AI threat detection |
|
IT System Failure (LMS / ERP outage) |
Avoid reliance on a single system |
System redundancy, backups, and failover systems |
Vendor SLAs and outsourcing agreements |
Accept short-duration outages |
Backup systems, IT support teams |
Cloud-native architecture, resilience testing |
|
Power Outage |
Avoid reliance on a single power source |
Backup generators, UPS systems |
Utility service agreements |
Accept short disruption |
Backup power systems, facility management |
Renewable energy integration, microgrid solutions |
|
Supply Chain Disruption (IT equipment / lab materials) |
Avoid single supplier dependency |
Multi-vendor sourcing, stockpiling critical items |
Supplier contracts with penalties |
Accept minor delays |
Approved vendor list, procurement policies |
Supplier risk monitoring, digital supply chain visibility |
|
Loss of Key Personnel (Faculty / IT Staff) |
Avoid a single point of dependency |
Cross-training, succession planning |
Outsourcing / contract staffing |
Accept temporary capability gaps |
HR policies, training programs |
Talent resilience planning, knowledge management systems |
|
Public Transport Disruption (Access to Campus) |
Avoid reliance on a single transport route |
Flexible schedules, remote work/learning |
N/A |
Accept commuting delays |
Online learning systems, communication channels |
Campus decentralisation, digital campus expansion |
|
Laboratory Equipment Failure |
Avoid outdated or unsupported equipment |
Preventive maintenance, calibration |
Vendor maintenance contracts |
Accept minor downtime |
Maintenance logs, equipment redundancy |
Predictive maintenance (IoT), digital twins |
|
Data Centre Outage |
Avoid single-site hosting |
Geographic redundancy, cloud backup |
Cloud service agreements |
Accept minimal downtime risk |
DR site, data replication |
Multi-cloud strategy, automated failover |
|
Terror Threat / Security Incident |
Avoid unsecured campus access |
Security screening, surveillance systems |
Insurance coverage |
Accept low probability events |
Security personnel, CCTV, access control |
Smart surveillance analytics, integrated command centre |
Legend
- Risk Avoidance: A Strategy to prevent risk from occurring entirely.
- Risk Reduction: Minimise the likelihood or impact through controls.
- Risk Transference: Shift impact to third parties (e.g., insurers).
- Risk Acceptance: Tolerating the risk as part of the business strategy.
- Existing Controls: Measures already implemented.
- Additional Controls: Planned improvements and new initiatives.
The treatment and control strategies outlined above demonstrate how the Singapore Institute of Technology can systematically strengthen its resilience against a broad spectrum of threats.
By aligning each crisis scenario with appropriate risk treatment options, SIT ensures that risks are either avoided, mitigated, transferred, or consciously accepted within defined tolerance levels.
Importantly, the integration of existing controls with forward-looking planned controls—such as AI-driven monitoring, predictive analytics, and cloud-based resilience—reflects a shift towards proactive and adaptive crisis management.
This approach is essential for SIT as it evolves into a digitally enabled, distributed campus environment.
Ultimately, this structured treatment framework supports SIT’s goal of maintaining operational continuity, safeguarding stakeholders, and sustaining academic excellence, even in the face of increasingly complex and interconnected risks.
More Information About Crisis Management Blended/ Hybrid Learning Courses
To learn more about the course and schedule, click the buttons below for the CM-300 Crisis Management Implementer [CM-3] and the CM-5000 Crisis Management Expert Implementer [CM-5].


![x [CM] [SIT] Title Banner](https://no-cache.hubspot.com/cta/default/3893111/ac11333b-2002-43b6-9cbf-a85a01f35ce1.png)
![[CM] [E3] [Risk Assessment] Treatment and Control](https://no-cache.hubspot.com/cta/default/3893111/0530af71-de87-4b68-9f41-28e11a970dfc.png)
![[CM] [SIT] Legal Disclaimer Banner](https://no-cache.hubspot.com/cta/default/3893111/7cd96343-be69-4196-84d6-73f1153f1d2f.png)
![[CM] [E3] [Risk Assessment] Treatment and Control](https://blog.bcm-institute.org/hs-fs/hubfs/RYT%20eBook%20Blog%20Banner/RYT%20E3%20Long%20Banner/%5BCM%5D%20%5BE3%5D%20%5BRisk%20Assessment%5D%20Treatment%20and%20Control.png?width=1920&height=220&name=%5BCM%5D%20%5BE3%5D%20%5BRisk%20Assessment%5D%20Treatment%20and%20Control.png)

![[CM] [GEN] [E3] [C1] Starting Your BCM Implementation](https://no-cache.hubspot.com/cta/default/3893111/a1d12928-4a0a-40a4-a390-6cd01a6f88ad.png)
![[CM] [SIT] [E3] [RAR] [T1-1] List of Threats](https://no-cache.hubspot.com/cta/default/3893111/b808b80d-150f-46e7-9ce1-905e66593ef5.png)
![[CM] [SIT] [E3] [RAR] [T1-2] List of Threats](https://no-cache.hubspot.com/cta/default/3893111/42c34692-d93d-443d-8064-83807c3f95a7.png)
![[CM] [SIT] [E3] [RAR] [P1-3] [Technology] List of Threats](https://no-cache.hubspot.com/cta/default/3893111/54bfa3cb-36bd-412b-9d0e-d961657215aa.png)
![[CM] [SIT] [E3] [RAR] [T3] Risk Impact and Likelihood Assessment](https://no-cache.hubspot.com/cta/default/3893111/7e6a7430-be49-4aa6-a58f-5dbdc4e3a482.png)
![[CM] [SIT] [E3] [CMS] [T1] Crisis Prevention Strategy](https://no-cache.hubspot.com/cta/default/3893111/e5370101-5bdd-4e4f-931d-25d53bd946f7.png)
![[CM] [SIT] [E3] [CMS] [T2] Crisis Response Strategy](https://no-cache.hubspot.com/cta/default/3893111/9eed27f2-9c27-4fca-b9c9-f270e2511e53.png)





![[BL-CM] [5] Register](https://no-cache.hubspot.com/cta/default/3893111/82024308-16f4-4491-98be-818a882c6286.png)

![Email to Sales Team [BCM Institute]](https://no-cache.hubspot.com/cta/default/3893111/3c53daeb-2836-4843-b0e0-645baee2ab9e.png)